North Korean hackers are using advanced AI methods for hacking corporate systems via human intervention, rather than relying on any technical vulnerability.
Zerion, the crypto wallet service, recently came forward with information regarding how its North Korean hacking affiliates conducted a prolonged social engineering attack and stole about $100,000 worth of funds stored in the company’s hot wallets.
On Wednesday, the Zerion team posted a comprehensive analysis stating that none of their customers were harmed, as their wallets, main apps, or core services remained unaffected by the breach. As a precautionary step, they shut down their web application.
Although the stolen amount is modest compared to many high-profile crypto incidents, Zerion described it as yet another example of an “AI-enabled social engineering attack linked to a DPRK threat actor.” This marks the second notable case this month involving similar tactics.
Just weeks earlier, the Drift Protocol suffered a massive $280–285 million exploit, also attributed to North Korean hacker groups through what was called a “structured intelligence operation.”
In both situations, the entry point wasn’t a smart contract flaw but rather carefully targeted individuals within the organizations. This shift shows how North Korean hackers are focusing on people as the weakest link in crypto security.
How Did North Korean Hackers Carry Out Zerion Exploit?
According to Zerion’s report, the intruders managed to access logged-in sessions and credentials of certain team members, eventually obtaining private keys to the company’s hot wallets.
“This incident showed that AI is changing the way cyber threats work,” the company noted. The approach mirrored other campaigns recently analyzed by the Security Alliance (SEAL), which has been actively tracking these activities. SEAL reported blocking 164 domains connected to the DPRK-linked group known as UNC1069 over a two-month period from February to April.
Hacker operations from North Korea normally employ prolonged, pressureless social engineering via platforms including Telegram, LinkedIn, and Slack. In such attacks, hackers usually pose as familiar colleagues or known companies or compromise existing accounts to establish credibility.
The approach has been described by experts as slow, calculated, and exploiting trust connections that already exist. For example, Google’s Mandiant division has noted the hackers’ use of fake Zoom sessions as well as artificial intelligence tools for modifying images and videos to enhance credibility.
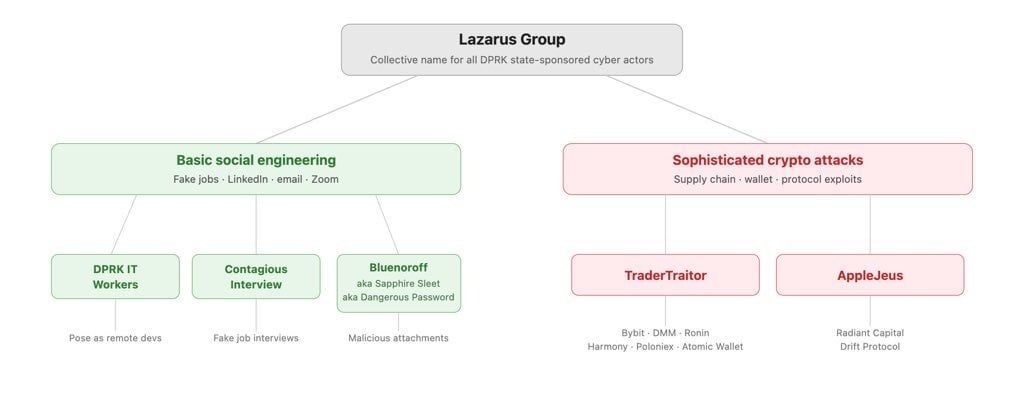
The Broader Evolution of DPRK Tactics
This isn’t a new phenomenon, but the integration of AI has taken it to another level. Blockchain security researchers at Elliptic pointed out earlier this year that North Korean hacker techniques have been developing for years. MetaMask developer and security expert Taylor Monahan noted that North Korean IT workers have been embedding themselves into crypto companies and DeFi projects for at least seven years.
“The evolution of the DPRK’s social engineering techniques, combined with the increasing availability of AI to refine and perfect these methods, means the threat extends well beyond exchanges,” Elliptic explained.
Individual developers, project contributors, and anyone with access to crypto infrastructure could now be in the crosshairs.
Security analysts often distinguish two main attack vectors used by these groups, one more advanced than the other. In simpler cases, basic phishing or credential harvesting could suffice, but in cases where a more complicated attack is needed, elaborate imitations, fabricated professional identities, and artificial intelligence scams that fool even experienced professionals become commonplace.
With North Korean hacker gangs increasingly relying on AI in such campaigns, the blockchain industry must recognize its own wakeup call. It is vital to acknowledge that although technical measures such as code reviews and multisig wallets are essential, they cannot stand alone.
The swift response from Zerion is an exemplary case that shows how immediate notification can reduce damage and provide valuable insights for the entire ecosystem.
That said, companies must invest heavily in employee awareness training, verify communications through multiple channels, and remain vigilant against unusual requests even from seemingly familiar contacts, especially as North Korea breeds North Korean hackers.